The rising exposure debt: 76% more bugs found, 46% fewer fixed, 25x critical backlog
TL;DR: Over the past twelve months, vulnerability submissions grew 76% and mean time to remediate dropped 80%. But total monthly fixes shipped fell 46%, the cumulative backlog grew over 21x, and unresolved criticals grew 25x. The MTTR improvement is largely a sample-selection artifact. Hard fixes did not finish slowly inside the average. They stopped finishing at all.
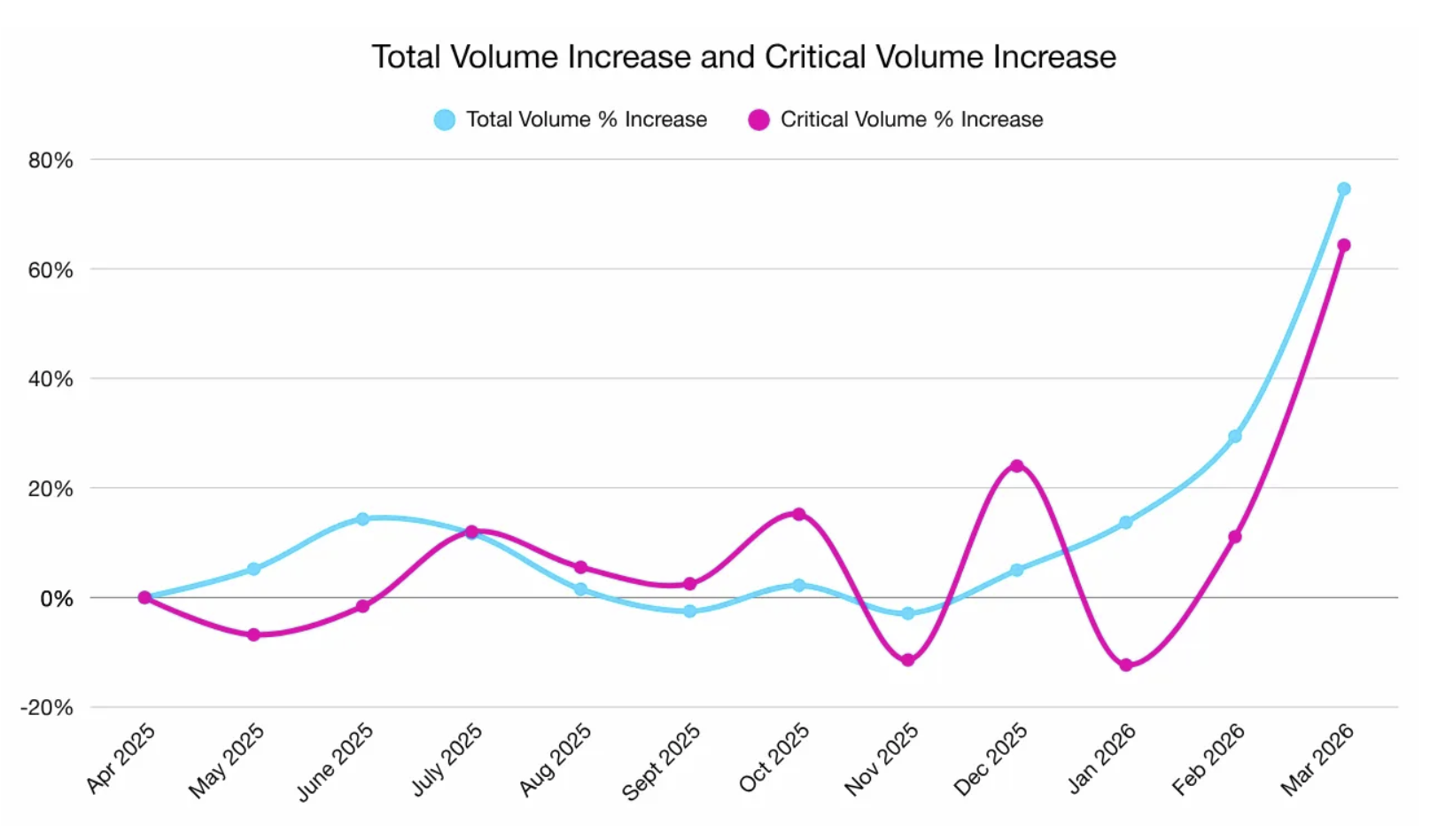
The headline numbers look like progress. Submissions up 76%. Mean time to remediate down 80%. Critical MTTR down 73%.
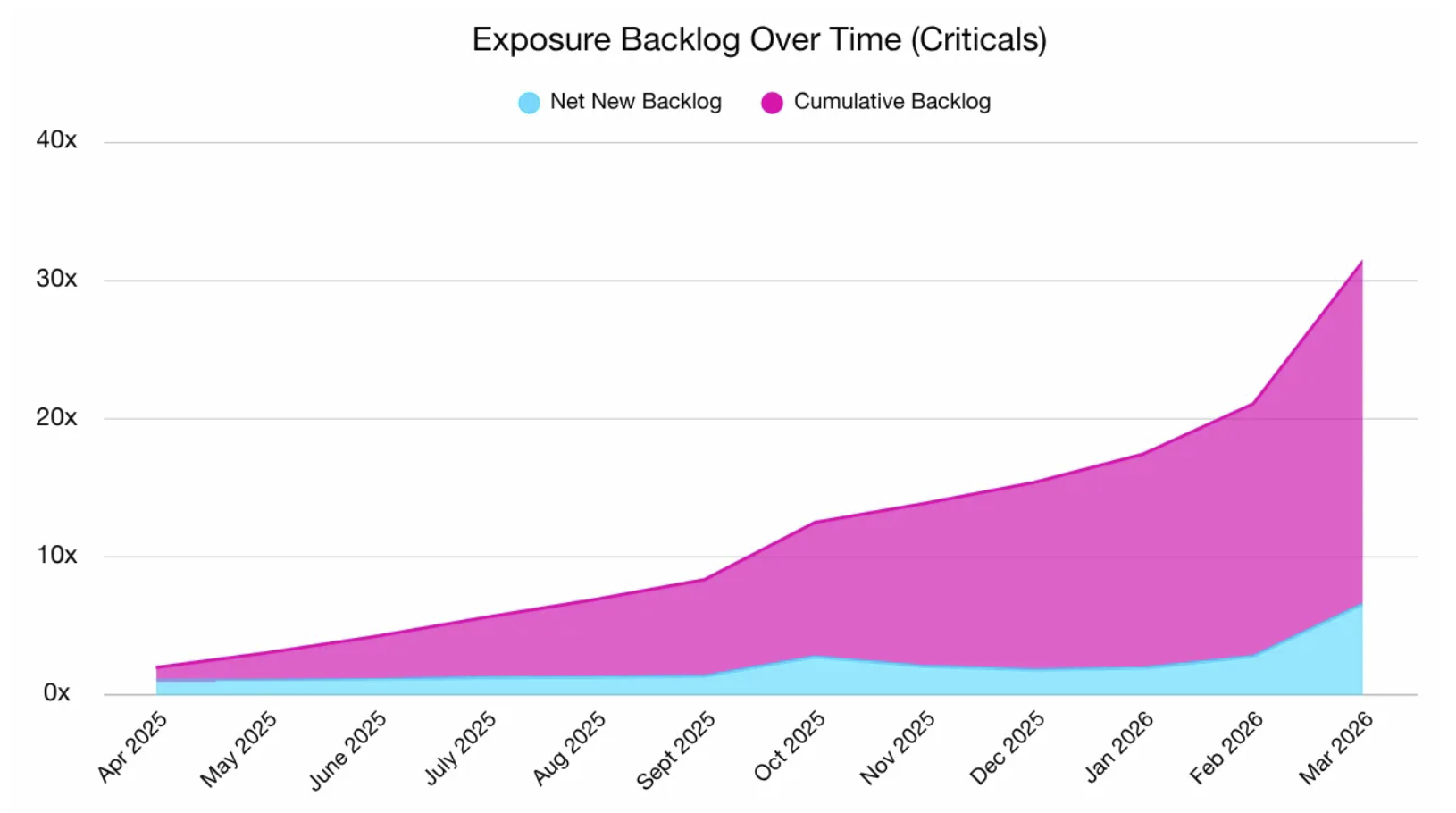
Total monthly fixes shipped fell 46%. The validated-but-unresolved backlog grew over 21x. Unresolved criticals grew 25x. Critical resolution rate fell from over 83% to under 40%.
More finds, fewer fixes, faster headline metrics, exploding backlog. The metrics are not contradicting each other. They are jointly describing a system that is bifurcating.
Highlights:
- Submissions grew approximately 76% in twelve months, driven by AI-assisted hunters who scale discovery at near-zero marginal cost.
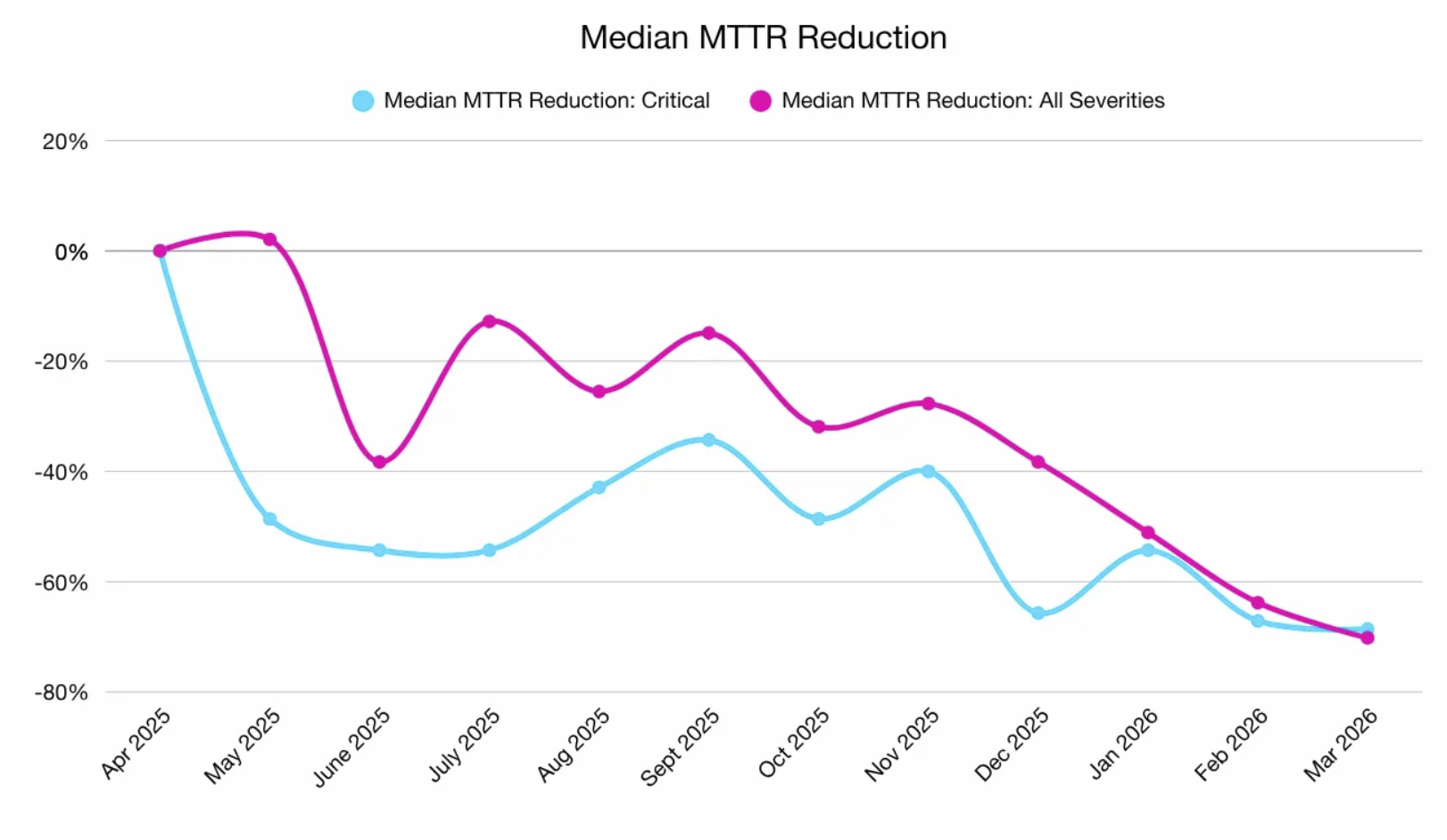
- Mean time to remediate dropped about 80%, median over 70%. The dashboard's headline win.
- Total monthly vulnerabilities resolved fell about 46% despite inflow rising 76%, so remediation throughput moved opposite to demand.
- Cumulative backlog grew more than 21x; unresolved criticals grew 25x, the fastest-growing and highest-impact slice.
- Critical resolution rate fell from over 83% to under 40%, so most criticals submitted today never reach a shipped fix.
My take:
- AI scaled vulnerability finding. Everyone with Claude Code is a hunter now, and frontier models have already shown they can find 500+ unknown bugs in heavily-fuzzed open-source projects. Bounties for critical issues are disproportionately larger, so people prioritize looking for them.
- AI scaled remediation, but not equally. The inequality is determined by remediation coordination complexity, not formal criticality. Isolated criticals are fixed faster with AI. But the remediation speed of the ones that require architectural changes, cross-team alignment, and upstream dependency fixes has remained the same or even slowed down.
- Another inequality driver is companies' engineering maturity. The ones with stable CI/CD, clear code ownership, and fast deployment have turbocharged remediation with AI. The ones primarily in the real sector haven't benefited from AI-assisted remediation much, but face a larger volume of vulnerabilities. As Mozilla's Firefox vulnerability win demonstrated, the AI defender advantage benefits firms that own their full stack.
Sources:
Finding Fast, Fixing Slow: The Rising Exposure Debt (May 2026)