Seven Priorities to Defend Against a Tireless Adversary
TLDR: AISI confirmed Mythos at 73% expert-CTF and end-to-end on a 32-step corporate takeover. $15k full attack cost. Seven priorities: update the threat model, inventory exposed systems, patch under 24 hours, reduce dependencies, AI security code review, five-incident tabletops, hard identity barriers.
Anthropic announced Claude Mythos Preview on Tuesday, April 7. The same week, CSA and SANS dropped a playbook, naming 13 risks and 11 priority actions on horizons from this-week to 12 months.
On the same beat, Anthropic told its own customers to patch internet-facing systems within 24 hours, drop SMS MFA, and run tabletop exercises for five simultaneous incidents instead of one.
Three things matter after the Mythos announcement. What is actually known about Mythos. What that changes versus how security programs run today. And what to prioritize, inspired by the CSA playbook and Anthropic's customer guidance.
Known details about Mythos.
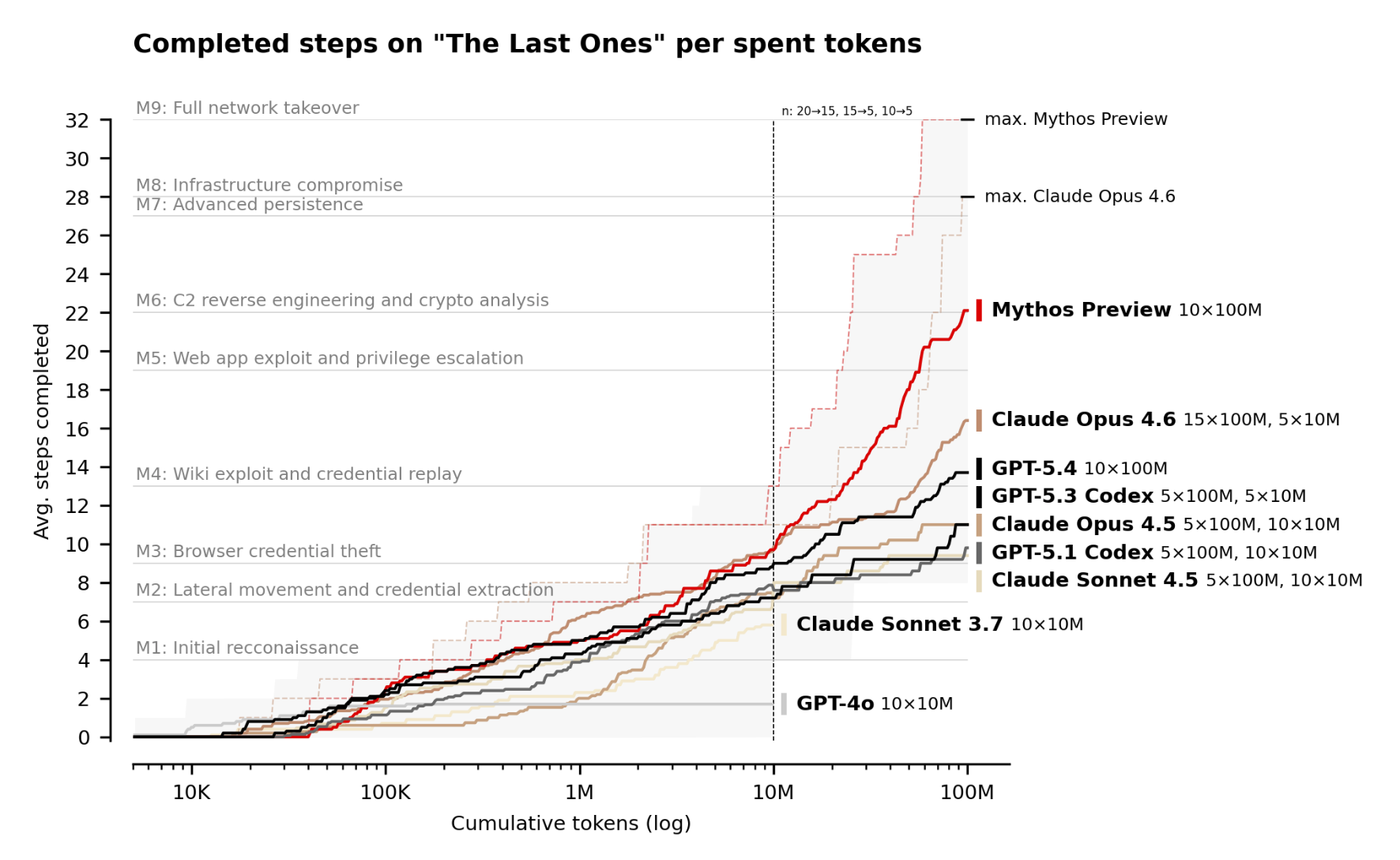
- The UK AI Security Institute ran Mythos through its cyber capability battery and published the results alongside the announcement. Mythos solved 73% of expert-CTFs and became the first model to complete AISI's 32-step corporate takeover simulation end-to-end.
- Caveats: these numbers assume no active defenders, no EDR, and no alerting penalty. Also, Mythos failed on the AISI OT range.
- Anthropic shared more dramatic figures. 181 working Firefox exploits in internal testing, where Opus 4.6 produced 2 under identical conditions. 'Thousands' of critical vulnerabilities across every major OS and browser. A 72% exploit success rate. A 27-year-old OpenBSD bug among them.
- The cost of Mythos-class discovery. Anthropic priced Mythos Preview at $25 per million input tokens and $125 per million output tokens. At those rates, a 100M-token AISI run costs $2.5k to $4.5k, and Mythos's 3-of-10 full-solve rate puts a 32-step takeover at $8k to $15k amortized. Anthropic's own OpenBSD sweep went the other way: a thousand smaller scaffold runs for under $20,000 total, surfacing one critical vulnerability plus several dozen more findings.
What Mythos is changing.
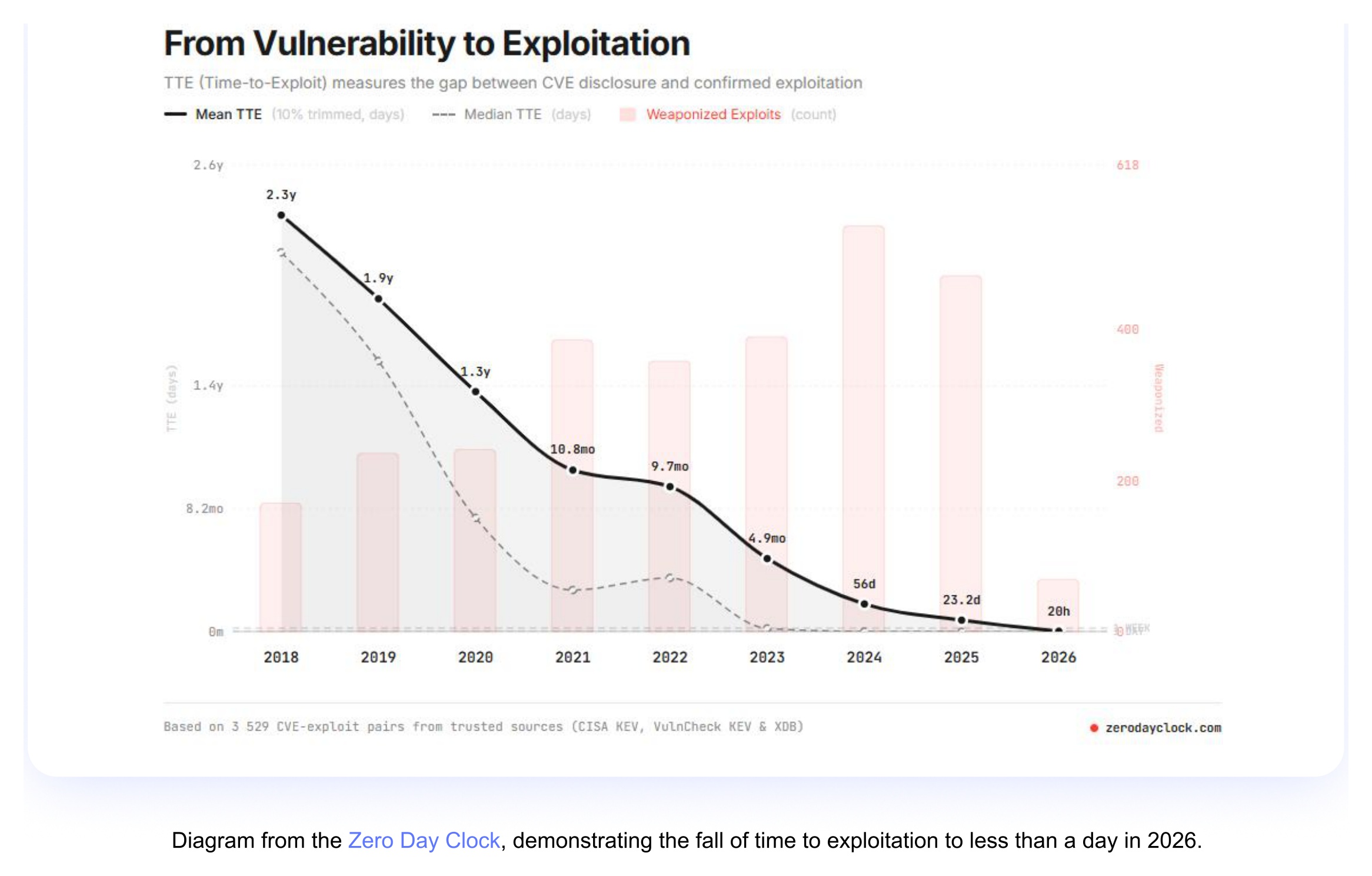
- The time-to-exploit has already collapsed from 2.3 years in 2018 to one day in 2026. Mythos will just accelerate it further.
- The attacker economics. The cost and time to find an exploitable vulnerability and conduct a targeted attack has reduced by ~10x, from hundreds of thousands of dollars to tens of thousands.
- Friction-based controls become ineffective. Anthropic names four: extra pivot hops, rate limits, non-standard ports, and SMS-based MFA. They worked by making attacks tedious for humans; AI grinds through tedium. Classical memory mitigations (ASLR, DEP, stack canaries) are a different case: they still raise the bar but less, since Mythos can autonomously chain multi-primitive memory-corruption exploits.
- Incident-response scope. The lower cost of attack increases the probability of simultaneous compromises. Traditional table-top exercises are for a single incident, not five simultaneous.
- Risk metrics and intel models. CVSS triage, Exploit Prediction Scoring System (EPSS) priors, and quarterly pen-testing baselines assumed weeks of attacker effort and are calibrated to a world that no longer exists. Pattern-based attribution weakens too. Exploits are becoming bespoke, so there are fewer reused signatures to match.
Seven things to prioritize.
1. Update the threat model to reflect the 10x improvement in the attacker economics. The old model priced attacker effort in expert-hours and treated multi-step chains as nation-state rare. If your company wasn't a lucrative target before, today it is.
2. The good old get to know your externally-facing systems. You cannot defend what you do not know about. Your external footprint has probably grown in the last year, as teams actively expose AI agents, MCP servers, and employee-built tools. Point an AI offensive agent at your own perimeter from outside, with no credentials and no source access, and let it fingerprint what is reachable and chain findings into a foothold.
3. Revise your patching cycle for internet-facing systems to under 24 hours. Treat any new CISA KEV entry as actively exploited within a business day, and prefer automated rollout over manual approval. Also, expect a CVE and patch flood, so build the operation to handle it with automated triage, deduplication, and patch validation.
4. Reduce your dependency surface. Open source is the number one attack target, as TeamPCP's supply-chain campaign demonstrated. Ask development teams to make a concerted effort to reduce dependencies. Make it fun and rewarding. If they use only a small part of a library or a package, maybe it's worth carefully vibe-coding it. Try to avoid re-writing the whole codebase.
5. Add AI-powered security code review at minimum. Run it on every PR so defense keeps pace with dev-team speed. Anthropic's Claude Code Security Review ships as a GitHub Action. Scope it narrowly: ANTHROPIC_API_KEY only, permissions contents: read, pull-requests: write, and a separate job not chained to build or deploy. See TeamPCP's supply-chain campaign for what happens otherwise.
6. Run tabletops for the real incident rate. Get ready for five simultaneous incidents. Establish emergency change procedures in advance: who can take a service offline, rotate a credential, or block a network path, and how fast.
7. Replace friction with hard barriers. Anthropic prescribes phishing-resistant MFA (FIDO2/passkeys) over SMS, attested hardware identity over shared passwords, short-lived scoped tokens over static API keys, and zero-trust between services. Segmentation is a backstop, not the lever.
Sources:
- The "AI Vulnerability Storm": Building a "Mythos-ready" Security Program (CSA, SANS, April 12, 2026)
- Our evaluation of Claude Mythos Preview's cyber capabilities (AISI, April 2026)
- Preparing Your Security Program for AI-Accelerated Offense (Anthropic, April 2026)
- Claude Mythos Preview (Anthropic, April 2026)
- Project Glasswing (Anthropic, April 2026)