Moltbot negotiated a car purchase. It scraped Reddit for pricing data, contacted dealers, handled email negotiations, and saved its owner $4,200 off a $56K sticker price
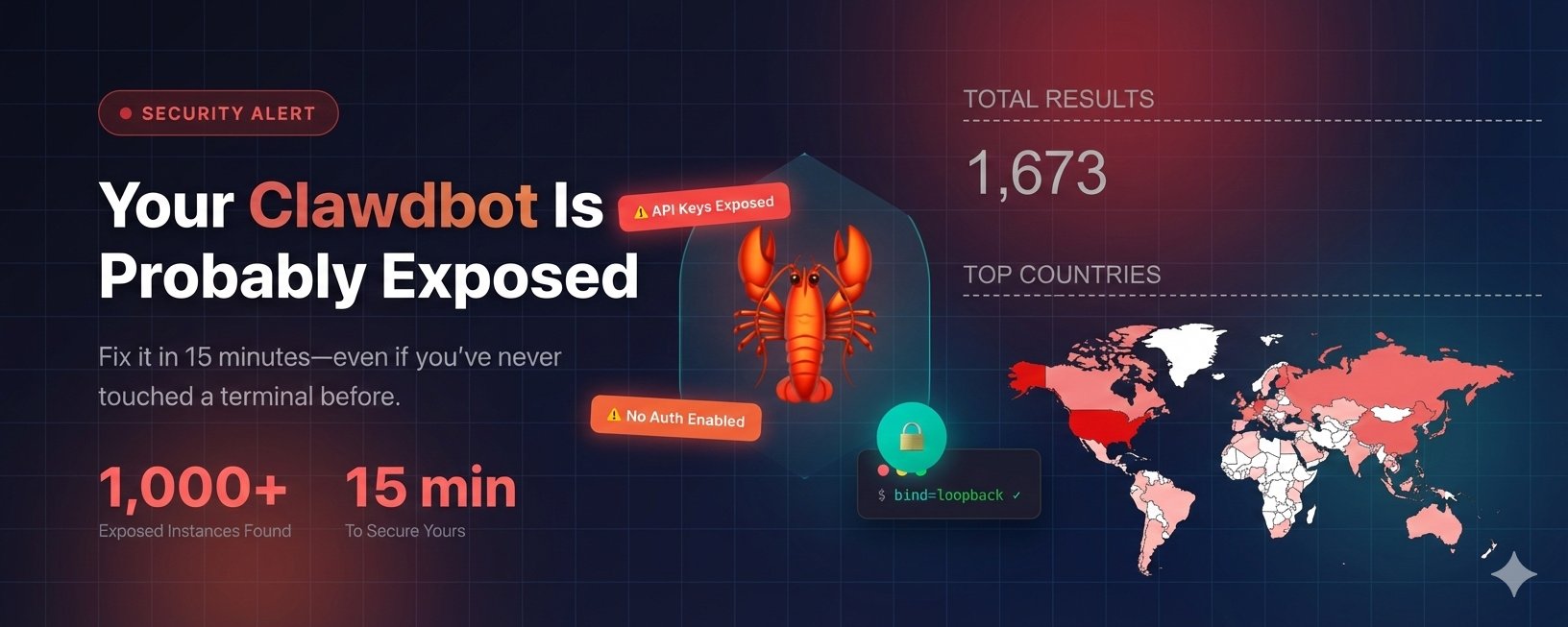
But the security issues are real. The former Clawdbot with 85K+ GitHub stars has some serious gaps:
- Credentials stored in plaintext files
- Exposed admin ports with no authentication
- No sandboxing — the AI gets full access to everything you do
- Complete conversation histories across Telegram, WhatsApp, Signal, and iMessage
- API keys for Claude, OpenAI, and other AI providers
- OAuth tokens and bot credentials
- Full shell access to the host machine
Some are reporting that enterprise employees are running this without IT knowing. I tend to believe it.
Quick summary of the hardening guide from NickSpisak_ on X:
- Bind gateway to localhost only ("bind": "loopback")
- Lock down file permissions — chmod 700 on config folders
- Disable mDNS/Bonjour network broadcasting
- Run clawdbot security audit --deep --fix
- Set up token or password authentication on the gateway
- Use Tailscale for remote access — never expose port 18789 publicly
- Update Node.js to 22.12.0+